I have seen stunningly bad habits from IT professionals regarding access, authentication, and general computing security. My favorites include using administrator auto-logon without a password, passwords such as “8675309” or just “password”, freely shared domain-level administrative accounts, the cliché sticky-notes on a monitor, and not updating known vulnerable software because something bad might happen.
Similarly, being work-from-home is not a guarantee of security if your teen child’s friend can, “just look something up on the web,” from your work computer. Remote workers and digital nomads need to consider the risks of an untended or unlocked laptop. Physical access to a computer makes hacking easier. You may not even notice an ultra-small USB thumb drive discreetly plugged into a laptop port. Certainly, do not trust a random USB drive you might find lying about.
Raspberry Robin gets the worm early (redcanary.com) – USB drives with malicious code.
The Cybersecurity & Infrastructure Security Agency (CISA) is on a month-long campaign promoting multi-factor authentication (MFA). Hooray, for MFA May! The added steps for authenticating a user and access can be inconvenient, but with good reasons. If nothing else, enable MFA to protect your financial and cloud-bases accounts and services.
To help you remember your passwords, I recommend an application like KeePass, with file support on multiple operating systems and phones.
Please, do not use the same password for every website. However, if you do, let me know it and I will add it to my own KeePass file just in case you forget it.
Regional and State-Sponsored Threats and Hacking
Hacking, phishing, and general espionage awareness
Operation CuckooBees: Cybereason Uncovers Massive Chinese Intellectual Property Theft Operation
Cisco Talos Intelligence Group – Comprehensive Threat Intelligence: Mustang Panda deploys a new wave of malware targeting Europe
Update on cyber activity in Eastern Europe (blog.google)
Trello From the Other Side: Tracking APT29 Phishing Campaigns | Mandiant
Threat actors based in China, Russia, Iran, and North Korea are among the most prolific. This week is no exception. Hackers target industries like telecom, tech, and manufacturing internationally, luring victims by phishing with topically ‘themed’ fake government reports and documents or engaging in directed espionage against diplomatic entities. This landscape of danger is always shifting.
Any traveling worker, whether self-employed or a corporate drone, is a potential mark for a threat actor. The reminder here is that no one is immune or invincible. Public work locations, internet cafés, and hotels make easy targets. When I do work in a public area, I make sure to prevent prying eyes from seeing my screen and I never leave my equipment unattended.
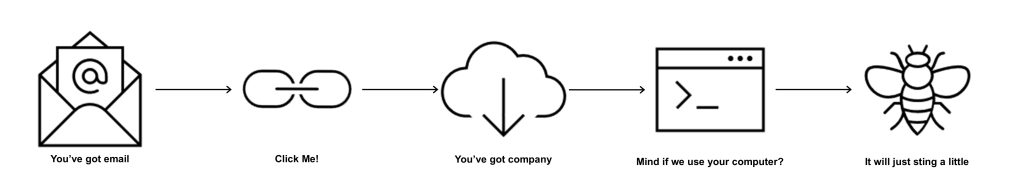
Malware and assailants may go unnoticed and under the radar for weeks or even years before detection methods catch on. I found suspicious malware once in a nine-month-old backup file set. Scrubbing the malware from the backup sets was insufficient. To be certain I was free from other undetected hacks required a complete wipe and reload of my work computer. I lost several days of productivity.
Recommendations and References:
Implement multi-factor authentication where possible, use a password ‘safe’, be vigilant and cautious especially in public spaces. Block onlookers. Do not use unfamiliar media. Keep your tools in your control. Keep your software up to date and backup data frequently.
Multi-Factor Authentication | CISA
Mozilla Firefox, Firefox ESR, Thunderbird
Security Vulnerability
Mozilla Releases Security Updates for Firefox, Firefox ESR, and Thunderbird | CISA
The modern web browser is the generic application of the world. Everyone uses one, everywhere, all the time, for everything. If you are using Firefox or Thunderbird, it is time to make an update.
A digital nomad or self-employed work-from-home freelancer takes on the responsibility to be their own IT department. There is often reluctance to allow updates to software for fear “something may break.” While a user’s trepidation is justified, the risks can be mitigated and manageable.
Save your work, backup your files, create a Windows restore point or Mac backup, and apply your updates. If your work is vital, have alternate means of access.
Recommendations and References:
Update to the latest available software.
Security Vulnerabilities fixed in Firefox 100 — Mozilla
Security Vulnerabilities fixed in Firefox ESR 91.9 — Mozilla
Security Vulnerabilities fixed in Thunderbird 91.9 — Mozilla
Avast and AVG Antivirus
Privilege Escalation of Code
Researchers Disclose Years-Old Vulnerabilities in Avast and AVG Antivirus (thehackernews.com)
Ten years, or maybe only six as stated in Avast’s release notes, is a long time for an undetected vulnerability. For a few of those years I recommended Avast, based on my experience and initially a recommendation by the late Jerry Pournelle.
Fortunately, there is no apparent evidence of exploitation in the wild. Nevertheless, a lack of evidence is not proof of security.
“Worryingly, the flaws could also be exploited as part of a second-stage browser attack or to perform a sandbox escape, leading to far-reaching consequences.” – TheHackerNews.com
As a side note: I find it musing when I browse to the linked article above from TheHackerNews.com about Avast, I see ads for McAfee antivirus software. Subtle.
Recommendations and References:
From the Avast release notes, update your software.
NEW Avast Version 22.1 (January 2022)